TOM FRANCIS
REGRETS THIS ALREADY
Hello! I'm Tom. I'm a game designer, writer, and programmer on Gunpoint, Heat Signature, and Tactical Breach Wizards. Here's some more info on all the games I've worked on, here are the videos I make on YouTube, and here are two short stories I wrote for the Machine of Death collections.
Search
Status
James was taken offline last week by my hosts, BlueHost, because something was spamming my database of posts incredibly rapidly with incredibly demanding data requests. It was using up so much CPU on the server that it was slowing down every other site it hosts.
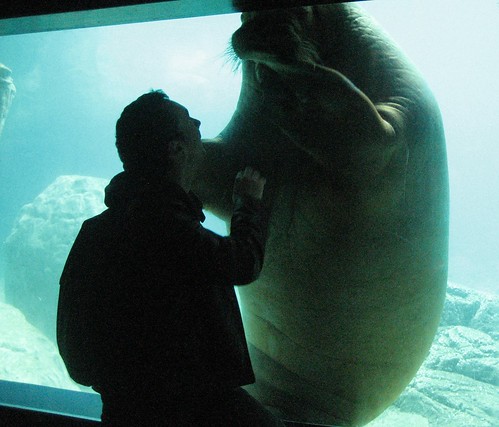
I was in New York meeting a nervous walrus at the time, so I couldn’t do much about it. Now that I’m back I’ve looked into it, done some maintenance, taken some precautions, and asked them to put it back online. The upshot is that it seems to be fixed for the time being, but I’m going to have to keep a very close eye on it for a while. If it goes down again, I’ll post updates on Twitter here.
If you’re interested in the technical specifics, here’s what I found:
- A few lines of malicious code have found their way back into my source code, despite my having changed my password and kept up to date with the latest WordPress updates since that last happened. I’ve removed them and changed my password again, to something ridiculous. Not sure if there’s anything I can do beyond that.
- One visitor, presumably robotic, immediately started loading the same page dozens of times a second within a few minutes of James going back up. I’ve banned its IP, but I don’t know how to prevent that kind of thing in general, or why it would cause slow SQL database queries.
- Something was accessing parts of the database that aren’t supposed to be public. After careful investigation I discovered that, on this occasion, it was myself: when I accessed the database directly to do some maintenance, it was taking 6 seconds or so just to display or select the tables. Further back, there are still calls to these private tables that I can’t explain. I choose to ignore both these problems.
Thanks for sticking around.
More Site Stuff